Introduction
Important before we start this lesson to thank the following people for helping writing the book and beign amazing friends!
Mayan Mohan
Alvin Argueta-Carpio
Niels Groeneveld
Luis Oliveira R.
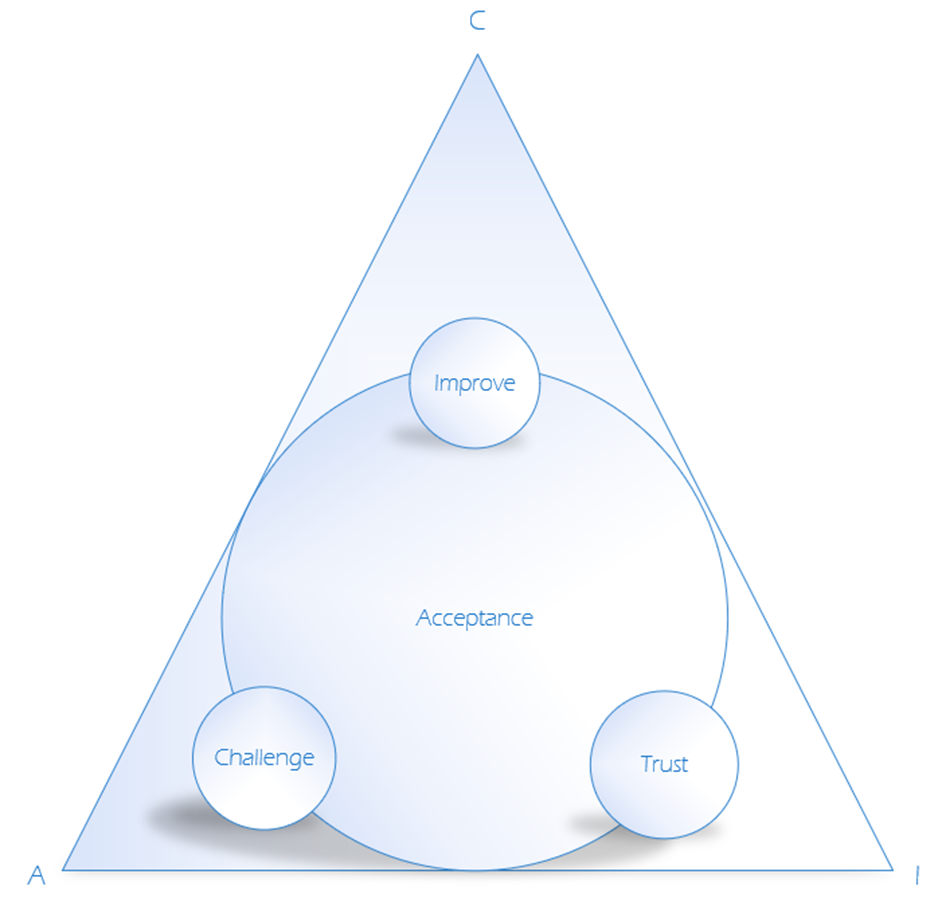
To continue our Journey in the CCSE we have to understand the core about what is security? and how can we give people a real sense of security? A good question one I hope to answer in 14 chapters. We usually follow the practice trust but verify, if you cannot trust it verify it if cannot be verified its not verifable so you can let it go. with this in mind we can easily build on top of this principle to improve our security model CIA Which has always been the backbone of any security system once one of the letters falls away the triangle will falter, So its important to see how you can make sure the systems you build adhere to these priniples.
To get back on track its important to also understand the moral implications of beign security expert in the field and the importance of understanding that not knowing is also knowing and you always can ask help as expert know where to find help for your problems. For cybersecurity we do have certain rules we try follow like the code, our mission is to do no harm. This comes originally from the medical field, where they take a Hippocratic oath to never hurt or mistreat a patient. We have something similar in cyber we call ethics where we are set by the rules and laws in the country we operate in and the company that will receive the assessment. Overall, it is a clever idea to make sure you are doing the right thing according to your circumstances.
To ensure the most effective protection of internet-connected systems, secure systems are essential for protecting data, systems, and networks. While these two concepts may appear similar at first glance, they have subtle differences that should be understood to ensure the most effective protection of internet-connected systems and offline systems.
Cybersecurity is defending the hardware and software from attack or unauthorized access is required and At the same time, information security is more comprehensive by including physical protection measures such as employee training or data access controls, while this covers other potential threats like malware attacks or system vulnerabilities that could compromise a business’s sensitive digital assets.
Organizations should consider cybersecurity and information security to develop a defensive strategy against cyber-attacks by malicious actors attempting to access confidential information. To achieve this, companies can implement robust authentication protocols with multiple-factor authentication, implement solid encryption techniques to stored data, and conduct regular staff training programs on effectively protecting their network and computer infrastructure.
Utilizing automated tools like vulnerability scanners can help identify any weak spots within the system architecture that need attention before it becomes too late. Usually, cybersecurity and information security are there to prevent the following things
- Use
- Disclosure
- Disruption
- Modification
- Destruction
- Denial
The importance of protecting information stored on digital or analog media cannot get overstated. Organizations must ensure their data’s confidentiality, integrity, and availability by implementing encryption, authentication protocols like multifactor authentication (MFA), and access control systems. Cybersecurity is an integral part of this effort, since it helps protect internet-connected systems from potential threats that could compromise sensitive information. As a result, the cybersecurity market has grown significantly in recent years to meet the growing demand for organizations to secure their data assets against malicious actors.
Fully safeguarding digital media from unauthorized access and other malicious activities requires a comprehensive security strategy encompassing both physical and digital elements. It should include policies governing user access privileges and endpoint protection solutions like antivirus software. These data loss protection (DLP) solutions can detect suspicious activity before it becomes too late for damage control measures to be effective. Additionally, organizations should consider investing in employee training programs, so they are aware of best practices when handling confidential information. Includes how not to become victims of phishing scams or other cyber-attacks targeting them directly.
Information Security
Organizations must adopt a proactive approach to information security, implementing comprehensive strategies that safeguard their data and ensure its proper utilization. This involves a multi-faceted approach encompassing both technological and procedural controls.
Robust authentication measures, such as multi-factor authentication (MFA) or biometric identification, are essential for restricting access to authorized personnel. Encryption technologies, utilizing salted hashes and secure algorithms, should be employed to protect confidential data in transit and at rest, whether it resides on networks, laptops, or mobile devices.
Continuous monitoring of systems is crucial to swiftly identify and address any suspicious activity. This early detection capability is key to preventing potential threats from escalating into full-blown security incidents.
Information security is not merely an IT concern; it’s a critical component of any organization’s overall risk management strategy. By prioritizing information security and implementing the appropriate policies and procedures, organizations can maintain a balance between data protection and authorized access. This proactive approach, coupled with vigilant monitoring, ensures that sensitive information remains secure while enabling the organization to operate effectively.
Source:
Information security – Wikipedia
Cybersecurity
According to the latest National Network and Information Security 2 (NIS2) regulation documentation is described as.
“Security of network and information systems’ means the ability of network and information systems to resist, at a given level of confidence, any event that may compromise the availability, authenticity, integrity or confidentiality of stored, transmitted or processed data or of the services offered by, or accessible via, those network and information systems;”
“NIS Directive.” ENISA, Accessed on 17 Jan. 2023, https://www.enisa.europa.eu/topics/cybersecurity-policy/nis-directive-new.
Cybersecurity is a multifaceted discipline, essential for safeguarding internet-connected systems from a wide array of threats. It encompasses a strategic combination of people, tools, policies, processes, and standards to prevent cyberattacks and unauthorized access.
Core Components of Cybersecurity:
- Prevention: Proactive measures aim to block attacks before they can compromise systems. These include:
- Firewalls: Filter network traffic and prevent unauthorized access.
- Intrusion Detection and Prevention Systems (IDPS): Monitor network activity for suspicious patterns and actively block potential threats.
- Antivirus Software: Scan files and emails for known malicious code.
- Data Encryption: Protects sensitive information by rendering it unreadable to unauthorized parties.
- Detection: Continuous monitoring of networks and systems is essential for identifying attacks that manage to bypass preventive measures. Cybersecurity professionals utilize tools like:
- Intrusion Detection Systems (IDS): Alert administrators to suspicious activity on the network.
- Security Information and Event Management (SIEM) Systems: Aggregate and analyze security logs from various sources to detect anomalies.
- Response and Mitigation: In the event of a detected attack, swift action is crucial to minimize damage. This includes:
- Incident Response Plans: Predefined procedures for containing and eradicating threats.
- Security Orchestration, Automation, and Response (SOAR) Platforms: Automate incident response tasks to accelerate remediation.
The Human Element:
Cybersecurity is not solely a technological challenge. User awareness and training are vital defenses against social engineering attacks, such as phishing scams. Educating users about best practices like strong passwords, two-factor authentication, and patch management is essential for reducing the risk of human error leading to security breaches.
Source:
The various kinds of cybersecurity teams
Usually, in cybersecurity, we have different teams with the objective of helping secure the organization. We are going to name the three most common ones.
The Blue Team
In the cybersecurity realm, the term “Blue Team” refers to a group of security professionals tasked with defending an organization’s network and systems from cyberattacks. These experts possess a broad spectrum of technical skills, specializing in areas such as:
- Network Security: Implementing and maintaining firewalls, intrusion detection systems (IDS), and other network security controls.
- Intrusion Detection: Monitoring network traffic and logs for signs of malicious activity.
- Incident Response: Quickly identifying and containing security breaches, minimizing damage, and restoring normal operations.
- Threat Hunting: Proactively searching for indicators of compromise (IOCs) and potential threats within the network.
- Vulnerability Management: Identifying and remediating vulnerabilities in systems and applications.
The Blue Team’s responsibilities are both proactive and reactive:
- Proactive: Hardening systems, implementing security controls, conducting security awareness training, and performing vulnerability assessments.
- Reactive: Responding to security alerts, investigating incidents, and remediating vulnerabilities exploited in attacks.
Blue Teams often collaborate with Red Teams (ethical hackers who simulate attacks) to identify weaknesses in the organization’s defenses and improve security posture. This collaboration is known as purple teaming, fostering a continuous cycle of improvement.
The Red Team
In contrast to the Blue Team’s defensive role, the “Red Team” takes on an offensive stance. This term, often used in military and security contexts, refers to a group of individuals whose mission is to simulate the actions of a potential adversary. Red Teams are tasked with testing the defenses of a target system or organization by attempting to breach security, identify vulnerabilities, and exploit weaknesses.
Members of a Red Team are typically highly skilled individuals with expertise in various areas, such as:
- Penetration Testing: Methodically probing systems for vulnerabilities and attempting to exploit them.
- Social Engineering: Using deception and manipulation to trick individuals into revealing confidential information or granting unauthorized access.
- Physical Security Testing: Assessing physical security controls, such as locks, alarms, and access procedures.
- Adversary Emulation: Mimicking the tactics, techniques, and procedures (TTPs) of real-world threat actors.
The goal of a Red Team is not simply to find vulnerabilities but to understand how those vulnerabilities could be exploited in a real-world attack scenario. By simulating attacks, Red Teams provide organizations with valuable insights into their security posture, enabling them to proactively address weaknesses and improve their overall defense capabilities.
Key Improvements:
- Clear Definition of Role: The text clearly defines the Red Team’s offensive role and its primary objectives.
- Emphasis on Expertise: The text highlights the specialized skills and knowledge possessed by Red Team members.
- Focus on Real-World Simulations: The text emphasizes the importance of simulating real-world attack scenarios to provide actionable insights.
- Concise and Professional Tone: The writing is streamlined and maintains a professional tone suitable for a technical audience.
The Purple Team
In the evolving landscape of cybersecurity, the “Purple Team” emerges as a collaborative force, merging the distinct roles of the Red and Blue Teams. This integrated approach brings together offensive and defensive security experts, working in unison to enhance an organization’s overall security posture.
The Purple Team’s primary objective is to provide a holistic view of an organization’s security landscape. This is achieved by combining the Red Team’s expertise in simulating attacks and identifying vulnerabilities with the Blue Team’s knowledge of defensive strategies and incident response. By working collaboratively, the Purple Team can:
- Identify and prioritize vulnerabilities: Leverage the Red Team’s offensive tactics to proactively uncover weaknesses in systems and applications.
- Test and improve security controls: Evaluate the effectiveness of existing security measures by simulating real-world attack scenarios.
- Enhance incident response capabilities: Use the Red Team’s insights to refine incident response plans and procedures.
- Strengthen security awareness: Educate employees about potential threats and best practices for maintaining a secure environment.
The Purple Team approach fosters a continuous cycle of improvement, where the insights gained from simulated attacks are used to enhance defenses, and the effectiveness of those defenses is then tested again. This iterative process helps organizations stay ahead of evolving threats and maintain a robust security posture.
Video:
Cybersecurity Teams – Red, Blue, Purple, Yellow, Orange, Green & White Team | information security
One Response
cool