Overview of Cybersecurity Frameworks
Understanding the relationship between cybersecurity and security is critical for asset protection. Below are definitions of the stakeholder roles and responsibilities in cybersecurity. Stakeholders play a vital role in facilitating collaboration among fellow stakeholders and providing guidance on addressing cybersecurity challenges.
A brief history of the Security standards timeline
There have been many important developments in computer security over the years. Here is a brief timeline of some key events:
- The National Bureau of Standards (now known as the National Institute of Standards and Technology, or NIST) was established in 1949.
- The first computer security conference was held in 1972 at the National Institute of Standards and Technology (NIST).
- The first version of the Federal Information Processing Standards (FIPS) was published in 1973. These standards establish minimum security requirements for federal computer systems.
- The Department of Defense (DOD) published the “Orange Book” in 1977, establishing standards for evaluating computer systems used in classified environments.
- The National Institute of Standards and Technology (NIST) publishes 1985 the first version of the “Guidelines for Computer Security Certification and Accreditation.”
- The Computer Security Act was passed, establishing the Computer Security Division within NIST in 1987. The Federal Information Security Management Act (FISMA) was passed and established in 1989 as a framework for protecting federal information and information systems.
- The Payment Card Industry Data Security Standard (PCI DSS) was established in 1990 to protect cardholder data.
- Sarbanes-Oxley Act was passed, establishing in 2002 new requirements for the protection of financial information and reporting security breaches.
- The International Organization for Standardization (ISO) published the ISO 27001 standard in 2005, which outlines requirements for an information security management system (ISMS).
- The National Institute of Standards and Technology (NIST) published in 2011 the first version of the Cybersecurity Framework (CSF), which provides guidelines for improving the security of critical infrastructure.
- The European Union (EU) enacts the General Data Protection Regulation (GDPR), which establishes 2013 new rules for protecting personal data.
- The National Institute of Standards and Technology (NIST) released 2016 the revised version of the Cybersecurity Framework (CSF), which includes updates to address emerging threats and technologies.
- The Payment Card Industry Data Security Standard (PCI DSS) is updated to version 3.2 in 2017.
- The National Institute of Standards and Technology (NIST) released in 2020 the revised version of the Cybersecurity Framework (CSF), which includes updates to address the evolving threat landscape and the increasing use of cloud computing and the Internet of Things (IoT).
This timeline provides a snapshot of some key developments in computer security over the years. There have been many other momentous events, and the field continues to evolve as modern technologies emerge and security threats evolve.
Cybersecurity Maturity Model Certification (CMMC)
To protect controlled unclassified information (CUI), the Department of Defense (DoD) developed a framework. Requiring contractors to meet certain cybersecurity standards and practices aims to increase the overall cybersecurity posture of contractors who work with the DoD.
CMMC is a tiered model with five levels of maturity ranging from basic cybersecurity practices to advanced and progressive. Each level builds upon the previous one, and the higher the level, the more robust and comprehensive the cybersecurity practices and controls must be.
Implementing CMMC in an organization requires a thorough understanding of the framework and the specific requirements for each level. The first step is determining the level required for the organization’s work with the DoD. It will depend on the type and sensitivity of the information the organization will handle at the required level. The organization must assess its current cybersecurity posture and identify gaps in meeting that level’s requirements. It may involve
- Risk assessment
- Implementing new controls
- Processes
- providing employee training.
An important aspect of implementing CMMC is developing a robust cybersecurity program integrated into the organization’s overall business processes. It includes establishing policies and procedures, implementing technical controls, and regularly testing and monitoring the effectiveness of these controls. One key element of a successful cybersecurity program is the involvement and commitment of top management. Senior leadership should be aware of and supportive of the efforts to implement CMMC and should prioritize cybersecurity in the organization’s overall risk management strategy.
In addition to implementing the technical controls and processes required by CMMC, organizations should also consider the human element of cybersecurity .including training employees on cybersecurity best practices and maintaining a culture of security within the organization. Finally, organizations should plan for ongoing maintenance and improvement of their cybersecurity program. Reviewing and updating policies and procedures, conducting regular risk assessments, and staying up to date on new threats and vulnerabilities. Implementing CMMC requires a significant investment of time and resources, but it is essential to protect the organization’s sensitive information and meet the requirements of the DoD. By following the steps outlined above and adopting a holistic approach to cybersecurity, organizations can successfully implement CMMC and improve their overall cybersecurity posture.
Source:
Video:
The Cybersecurity Maturity Model Certification (CMMC) In a Nutshell
NIST Cybersecurity Framework
The National Institute of Standards and Technology (NIST) Cybersecurity Framework is a set of guidelines and best practices for managing cybersecurity risks. It was developed by NIST, a non-regulatory agency of the United States Department of Commerce, in response to an executive order from the President of the United States. The NIST Cybersecurity Framework provides a common language and framework for organizations to use when developing, implementing, and improving their cybersecurity programs. It consists of five core functions.
- Identity
- Protect
- Detect
- Respond
- Recover
These functions get supported by a set of underlying categories and subcategories that provide more detailed guidance on specific cybersecurity activities and practices. The NIST Cybersecurity Framework is voluntary and intended to be used by organizations of all sizes and industries.
Cybersecurity Framework | NIST
Video:
Virtual Session: NIST Cybersecurity Framework Explained
A framework is a risk-based approach to reducing cybersecurity risk. The NIST Cybersecurity Framework consists of the Framework Core, the Framework Profile, and the Framework Implementation Tiers.
- Framework Core: A set of common cybersecurity activities across critical infrastructure sectors organized around particular outcomes. It comprises four components: Functions, Categories, Subcategories, and Informative References.
- Framework Profile: A representation of the outcomes that a particular system or organization has selected from the Framework Categories and Subcategories.
- Framework Implementation Tiers: An organization’s approach to risk – how an organization views cybersecurity risk and the processes in place to manage that risk.
Five Core Functions Overview
The core functions provide a high-level, strategic view of cybersecurity risk management.
- Identify – Develop an organization’s understanding to manage cybersecurity risk to systems, people, assets, data, and capabilities.
- Protect – Develop and implement appropriate safeguards to ensure the delivery of critical services.
- Detect – Develop and implement appropriate activities to identify the occurrence of a cybersecurity event.
- Respond – Develop and implement appropriate activities to act regarding a detected cybersecurity incident.
- Recover – Develop and implement appropriate activities to normal operations to reduce the impact of a cybersecurity incident.
Breakdown of Function Categories & Subcategories
Identify (ID)
- Asset Management (ID.AM) – The data, personnel, devices, systems, and facilities that enable the organization to achieve business purposes are identified and managed consistent with their relatively critical to organizational objectives and the organization’s risk strategy.
- ID.AM-1: Physical devices and systems within the organization are inventoried.
- ID.AM-2: Software platforms and applications within the organization are inventoried.
- ID.AM-3: Organizational communication and data flows are mapped.
- ID.AM-4: External information systems are cataloged.
- ID.AM-5: Resources (e.g., hardware, devices, data, time, personnel, and software) are prioritized based on their classification, criticality, and business value.
- ID.AM-6: Cybersecurity roles and responsibilities for the entire workforce and third-party stakeholders (e.g., suppliers, customers, partners) are established.
- Business Environment (I’D.BE) – The organization’s mission, objectives, stakeholders, and activities are understood and prioritized; this information is used to inform cybersecurity roles, responsibilities, and risk management decisions.
- I’D.BE-1: The organization’s role in the supply chain is identified and communicated.
- I’D.BE-2: The organization’s place in critical infrastructure and its industry sector is identified and communicated.
- I’D.BE-3: Priorities for organizational mission, objectives, and activities are established and communicated.
- ID.BE-4: Dependencies and critical functions for the delivery of critical services are established.
- I’D.BE-5: Resilience requirements to support the delivery of critical services are established for all operating states (e.g., under duress/attack, during recovery, and during normal operations).
- Governance (ID.GV) – The policies, procedures, and processes to manage and monitor the organization’s regulatory, legal, risk, environmental, and operational requirements are understood and inform the management of cybersecurity risk.
- ID.GV-1: Organizational cybersecurity policy is established and communicated.
- ID.GV-2: Cybersecurity roles and responsibilities are coordinated and aligned with internal roles and external partners.
- ID.GV-3: Legal and regulatory requirements regarding cybersecurity, including privacy and legal liberties obligations, are understood and managed.
- ID.GV-4: Governance and risk management processes address cybersecurity risks.
- Risk Assessment (ID.RA) – The organization understands the cybersecurity risk to organizational operations (including mission, functions, image, or reputation), organizational assets, and individuals.
- ID.RA-1: Asset vulnerabilities are identified and documented
- ID.RA-2: Cyber threat intelligence is received from information-sharing forums and sources.
- ID.RA-3: Threats, both internal and external, are identified and documented.
- ID.RA-4: Potential business impacts and likelihoods are identified.
- ID.RA-5: Threats, vulnerabilities, likelihoods, and impacts are used to determine risk.
- ID.RA-6: Risk responses are identified and prioritized.
- Risk Management Strategy (ID.RM) – The organization’s priorities, constraints, risk tolerances, and assumptions are established and used to support operational risk decisions.
- ID.RM-1: Risk management processes are established, managed, and agreed to by organizational stakeholders.
- ID.RM-2: Organizational risk tolerance is determined and clearly expressed.
- ID.RM-3: The organization’s determination of risk tolerance is informed by its role in critical infrastructure and sector-specific risk analysis.
- Supply Chain Risk Management (ID.SC) – The organization’s priorities, constraints, risk tolerances, and assumptions are established and used to support risk decisions associated with managing supply chain risk. The organization has established and implemented the processes to identify, assess, and manage supply chain risks.
- ID.SC-1: Cyber supply chain risk management processes are identified, established, assessed, managed, and agreed to by organizational stakeholders.
- ID.SC-2: Suppliers and third-party partners of information systems, components, and services are identified, prioritized, and accessed using a cyber supply chain risk assessment process.
- ID.SC-3: Contracts with suppliers and third-party partners are used to implement appropriate measures designed to meet the objectives of an organization’s cybersecurity program and Cyber supply Chain Risk Management Plan.
- ID.SC-4: Supplies and third-party partners are routinely assessed using audits, test results, or other forms of evaluations to confirm they are meeting their contractual obligations.
- ID.SC-5: Response and recovery planning are testing conducted with suppliers and third-party providers.
Protect (PR)
- Identify Management and Access Control (PR.AC) – Access to physical and logical assets and associated facilities is limited to authorized users, processes, and devices, and is managed consistent with the assessed risk of unauthorized access to authorized activities and transactions.
- PR.AC-1: Identifies and credentials are issued, managed, verified, revoked, and audited for authorized devices, users, and processes.
- PR.AC-2: Physical access to assets is managed and protected.
- PC.AC-3: Remote access is managed.
- PC.AC-4: Access permissions and authorizations are managed, incorporating the principles of least privilege and separation of duties.
- PR.AC-5: Network integrity is protected (e.g., network segregation, network segmentation).
- PR.AC-6: Identities are proofed and bound to credentials and asserted in interactions.
- PR.AC-7: Users, devices, and other assets are authenticated (e.g., single-factor, multi-factor) commensurate with the risk of the transaction (e.g., individual’s security and privacy risks and other organizational risks).
- Awareness and Training (PR.AT) – The organization’s personnel and partners are provided cybersecurity awareness education and are trained to perform their cybersecurity-related duties and responsibilities consistent with related policies, procedures, and agreements.
- PR.AT-1: All users are informed and trained.
- PR.AT-2: Privileged users understand their roles and responsibilities.
- PR.AT-3: Third-party stakeholders (e.g., suppliers, customers, partners) understand their roles and responsibilities.
- PR.AT-4: Senior executives understand their roles and responsibilities.
- PR.AT-5: Physical and cybersecurity personnel understand their roles and responsibilities.
- Data Security (PR.DS) – Information and records (data) are managed consistently with the organization’s risk strategy to protect confidentiality, integrity, and availability of information.
- PR.DS-1: Data-at-rest is protected
- PR.DS-2: Data-in-transit is protected
- PR.DS-3: Assets are formally managed throughout removal, transfers, and disposition.
- PR.DS-4: Adequate capacity to ensure availability is maintained.
- PR.DS-5: Protections against data leaks are implemented.
- PR.DS-6: Integrity-checking mechanisms are used to verify software, firmware, and information integrity.
- PR.DS-7: The development and testing environment(s) are separate from the production environment.
- PR.DS-8: Integrity-checking mechanisms are used to verify hardware integrity.
- Information Protection Processes and Procedures (PR.IP) – Security policies (that address purpose, scope, roles, responsibilities, management commitment, and coordination among organizational entities), processes, and procedures are maintained and used to manage the protection of information systems and assets.
- PR.IP-1: A baseline configuration of information technology/industrial control systems is created and maintained incorporating security principles (e.g., concept of least functionality).
- PR.IP-2: A System Development Life Cycle to manage systems is implemented.
- PR.IP-3: Configuration change control processes are in place.
- PR.IP-4: Backups of information are conducted, maintained, and tested.
- PR.IP-5: Policy and regulations regarding the physical operating environment for organizational assets are met.
- PR.IP-6: Data is destroyed according to policy.
- PR.IP-7: Protection processes are improved.
- PR.IP-8: Effectiveness of protection technologies is shared.
- PR.IP-9: Response plan (Incident Response and Business Continuity) and recovery plans (Incident Response and Disaster Recovery) are in place and managed.
- PR.IP-10: Response and recovery plans are tested.
- PR.IP-11: Cybersecurity is included in human resources practices (e.g., deprovisioning, personnel screening).
- PR.IP-12: A vulnerability management plan is developed and implemented.
- Maintenance (PR.MA) – Maintenance of repairs of industrial control and information system components are performed consistent with policies and procedures.
- PR.MA-1: Maintenance and repair of organizational assets are performed and logged, with approved and controlled tools.
- PR.MA-2: Remote maintenance of organizational assets is approved, logged, and performed in a manner that prevents unauthorized access.
- Protective Technology (PR.PT) – Technical security solutions are managed to ensure the security and resilience of systems and assets, consistent with related policies, procedures, and agreements.
- PR.PT-1: Audit/log records are determined, documented, implemented, and reviewed in accordance with policy.
- PR.PT-2: Removable media is protected, and its use is restricted according to policy.
- PR.PT-3: The principle of least functionality is incorporated by configuring systems to provide only essential capabilities.
- PR.PT-4: Communications and control networks are protected.
- PR.PT-5: Mechanisms (e.g., failsafe, load balancing, hot swap) are implemented to achieve resilience requirements in normal and adverse situations.
Detect (DE)
- Anomalies and Events (DE.AE) – Anomalous activity is detected, and the potential impact of events is understood.
- DE.AE-1: A baseline of network operations and expected data flows for users, and systems are established and managed.
- DE.AE-2: Detected events are analyzed to understand attack targets and methods.
- DE.AE-3: Event data are collected and correlated from multiple sources and sensors.
- DE.AE-4: The impact of events is determined.
- DE.AE-5: Incident alert thresholds are established.
- Security Continuous Monitoring (DE.CM) – The information system and assets are monitored to identify cybersecurity events and verify the effectiveness of protective measures.
- DE.CM-1: The network is monitored to detect potential cybersecurity events.
- DE.CM-2: The physical environment is monitored to detect potential cybersecurity events.
- DE.CM-3: Personnel activity is monitored to detect potential cybersecurity events.
- DE.CM-4: Malicious code is detected.
- DE.CM-5: Unauthorized mobile code is detected.
- DE.CM-6: External service provider activity is monitored to detect potential cybersecurity events.
- DE.CM-7: Monitoring for unauthorized personnel, connections, devices, and software is performed.
- DE.CM-8: Vulnerability scans are performed.
- Detection Processes (DE.DP) – Detection processes and procedures are maintained and tested to ensure awareness of abnormal events.
- DE.DP-1: Roles and responsibilities for detection are well-defined to ensure accountability.
- DE.DP-2: Detection activities comply with all applicable requirements.
- DE.DP-3: Detection processes are tested.
- DE.DP-4: Event detection information is communicated.
- DE.DP-5: Detection processes are continuously improved.
Respond (RS)
- Response Planning (RS.RP) – Response processes and procedures are executed and maintained, to ensure a response to detected cybersecurity incidents.
- RS.RP-1: A response plan is executed during or after an incident.
- Communications (RS.CO) – Response activities are coordinated with internal and external stakeholders (e.g., external support from law enforcement agencies).
- RS.CO-1: Personnel knows their roles and order of operations when a response is needed.
- RS.CO-2: Incidents are reported consistent with established criteria.
- RS.CO-3: Information is shared consistent with response plans.
- RS.CO-4: Coordination with stakeholders occurs consistent with response plans.
- RS.CO-5: Voluntary information sharing occurs with external stakeholders to achieve broader cybersecurity situational awareness.
- Analysis (RS.AN) – Analysis is conducted to ensure effective response and support recovery activities.
- RS.AN-1: Notifications from detection systems are investigated.
- RS.AN-2: The impact of the incident is understood.
- RS.AN-3: Forensics are performed.
- RS.AN-4: Incidents are categorized consistently with response plans.
- RS.AN-5: Processes are established to receive, analyze and respond to vulnerabilities disclosed to the organization from internal and external sources (e.g., internal testing, security bulletins, or security researchers).
- Mitigation (RS.MI) – Activities are performed to prevent the expansion of an event, mitigate its effects, and resolve the incident.
- RS.MI-1: Incidents are contained.
- RS.MI-2: Incidents are mitigated.
- RS.MI-3: Newly identified vulnerabilities are mitigated or documented as accepted risks.
- Improvements (RS.IM) – Organizational response activities are improved by incorporating lessons learned from current and previous detection/response activities.
- RS.IM-1: Response plans incorporate lessons learned.
- RS.IM-2: Response strategies are updated.
Recover (RC)
- Recovery Planning (RC.RP) – Recovery processes and procedures are executed and maintained to ensure the restoration of systems or assets affected by cybersecurity incidents.
- RC.RP-1: A recovery plan is executed during or after a cybersecurity incident.
- RC.RP-2: Recovery strategies are updated.
- Improvements (RC.IM) – Recovery planning and processes are improved by incorporating lessons learned into future activities.
- RC.IM-1: Recovery plans incorporate lessons learned.
- RC.IM-2: Recovery strategies are updated.
- Communications (RC.CO) – Restoration activities are coordinated with internal and external parties (e.g., coordinating centers, Internet Service Providers, owners of attacking systems, victims, other CSIRTs, and vendors).
- RC.CO-1: Public relations are managed.
- RC.CO-2: Reputation is repaired after an incident.
- RC.CO-3: Recovery activities are communicated to internal and external stakeholders and executive and management teams.
Informative Reference
A specific section of standards, guidelines, and practices common among critical infrastructure sectors that illustrates a method to achieve the outcomes associated with each Subcategory. For a list of Informative References, please visit the Informative References column in Table 2: Framework Core of the Cybersecurity Framework.
Framework Profile
A Framework Profile allows organizations to establish a roadmap for reducing cybersecurity risks. Conducting a profile assessment can reveal the current state of your organization about the Cybersecurity Framework. The framework can also be used to develop the desired profile that you would like to achieve. By comparing the current state and the desired state, you can identify the “gaps” in your profile. The gaps serve as objectives for improvement. These gaps can be addressed by consulting the appropriate Informative Reference materials.
Framework Implementation Tiers
- Tiers describe an organization’s risk and controls.
Tier 1: Partial
- Risk Management Process – Organizational cybersecurity risk management practices are not formalized, and risk is managed ad hoc and sometimes reactive.
- Integrated Risk Management Program – There is limited awareness of cybersecurity risk at the organizational level.
- External Participation – The organization does not understand its role in the larger ecosystem concerning either its dependencies or dependents.
Tier 2: Risk Informed
- Risk Management Process – Risk management practices are approved by management but may not be established as organizational-wide policy.
- Integrated Risk Management Process – There is an awareness of cybersecurity risk at the organizational level, but an organization-wide approach to managing cybersecurity risk has not been established.
- External Participation – Generally, the organization understands its role in the larger ecosystem with respect to either its own dependencies or dependents, but not both.
Tier 3: Repeatable
- Risk Management Process – The organization’s risk management practices are formally approved and expressed as policy.
- Integrated Risk Management Program – There is an organization-wide approach to managing cybersecurity risk.
- External Participation – The organization understands its role, dependencies, and dependents in the larger ecosystem and may contribute to the community’s broader understanding of risks.
Tier 4: Adaptive
- Risk Management Process – The organization adapts its cybersecurity practices based on previous and current cybersecurity activities, including lessons learned and predictive indicators.
- Integrated Risk Management Program – There is an organization-wide approach to managing cybersecurity risk that uses-informed policies, processes, and procedures to address potential cybersecurity events.
- External Participation – The organization understands its role, dependencies, and dependents in the larger ecosystem and contributes to the community’s border understanding of risk.
NIST FIPS 199 “Standards for Security Categorization of Federal Information and Information Systems
- Low Impact – The loss of confidentiality, integrity, or availability could be expected to have a limited adverse effect on organizational operations, organizational assets, or individuals.
- (i) cause degradation in mission capability to an extent and duration that the organization can perform primary functions, but the effectiveness is noticeably reduced
- (ii) result in minor damage to organizational assets
- (iii) result in minor monetary loss
- (iv) result in minor harm to individuals
- Medium Impact – The loss of confidentiality, integrity, or availability could be expected to have a serious adverse effect on organizational operations, organizational assets, or individuals.
- (i) cause significant degradation in mission capability to an extent and duration that the organization can perform its primary functions, but the effectiveness of the functions is significantly reduced
- (ii) result in considerable damage to organizational assets
- (iii) result in significant monetary loss
- (iv) result in significant harm to individuals that does not involve loss of life or serious life-threatening injuries
- High Impact – The loss of confidentiality, integrity, or availability could be expected to have a severe or catastrophic adverse effect on organizational operations, organizational assets, or individuals.
- (i) cause a severe degradation in or loss of mission capability to an extent or duration that the organization is not able to perform one or more of its primary functions
- (ii) result in major damage to organizational assets
- (iii) result in major monetary loss
- (iv) result in severe or catastrophic harm to individuals involving loss of life or serious life-threatening injuries
“Adverse effects on individuals may include, but are not limited to, loss of the privacy to which individuals are entitled under the law (Public Law 104-13)” as cited in FIPS.
Source: “Potential Impacts Definitions for Security Objectives” FIPS 199
NIST SP 800-30 “Guide for Conducting Risk Assessments”
NIST SP 800-30 “Guide for Conducting Risk Assessments is composed of four steps: prepare for the risk assessment, conduct the assessment, communicate and share risk assessment information, and maintain the risk assessment. Preparing for the risk assessment establishes the context for the risk assessment. Conducting the assessment results in a list of information security risks that can be prioritized by risk level and is used to inform risk response decisions. Communicating and sharing risk assessment information ensures that decision makers across the organization have the appropriate risk-related information needed to inform and guide risk decisions. Maintaining the risk assessment involves keeping current and specific knowledge of risks faced by the organization.
Step 1: Prepare for the Risk Assessment
- Identify the purpose of the assessment
- Identify the scope of the assessment
- Identify the assumptions and constraints associated with the assessment
- Identify the sources of information to be used as inputs to the assessment
- Identify the risk a model and analytic approaches (i.e., assessment and analysis approaches) to be employed during the assessment
Identify the Purpose
of the risk assessment in terms of the information that the assessment is intended to produce and the decisions the assessment is intended to support.
- (i) an initial assessment
- (i) establishing a baseline assessment of risk
- (ii) identifying threats and vulnerabilities, impacts to organizational operations and assets, individuals, other organizations, the Nation, or other risk factors tracked over time as part of risk monitoring
- (ii) initiated from risk response or monitoring steps outlined in risk management
- (i) Ongoing determinations of the ongoing effectiveness of security controls in organization information systems or environment of operations
- (ii) Changes to information systems or environments of operation (e.g., changes to hardware, firmware, software; changes to system-specific, hybrid, or common controls, changes to mission/business processes, common infrastructure and support services, threats, vulnerabilities, or facilities
- (iii) Results from compliance verification activities.
- Reassessment due to incidents occurring (e.g., cyber-attacks compromising organizational information or information systems).
Identify Scope
Identify the scope of the risk assessment in terms of organizational applicability, time frame supported, and architectural/technology considerations. The scope of the assessment determines what will be considered in the assessment.
- Organizational Applicability – Describes which parts of the organization or sub organizations are affected by the risk assessment and the risk-based decisions resulting from the assessment.
- Effectiveness Time Frame – Determines how long the results of a detailed risk assessment can be used to inform risk-based decisions legitimately.
- Architectural/Technology Considerations – Clarify the scope of the risk assessment.
- Tier 3: Includes organizational information systems in its environment of operations (vulnerabilities in inherited controls are taken into consideration)
- Tier 2: Defined by mission/business segment architecture (e.g., all systems, services, and infrastructure that support a specific mission/function)
- Tier 1: Answer a specific question (test and specific technology).
Identify Assumptions and Constraints
Identify the specific assumptions and constraints under which the risk assessment is conducted.
- Threat Sources:
- Threat Events:
- Vulnerabilities and Predisposing Conditions:
- Likelihood:
- Impacts:
- Risk Tolerance and Uncertainty:
- Analytic Approach:
Identify Information Sources
Identify the sources of descriptive, threat, vulnerability, and impact information to be used in the risk assessment.
Identify Risk Model and Analytic Approach
Identify the risk model and analytic approach to be used in the risk assessment.
Step 2: Conduct the Assessment
Conducting the assessment produces a list of information security risks that can be prioritized by risk level and used to inform risk response decisions.
- Identify threat sources that are relevant to organizations
- Identify threat events that could be produced by those sources
- Identify vulnerabilities within organizations that could be exploited by threat sources through specific threat events and the predisposing conditions that could affect successful exploitation
- Determine the likelihood that the identified threat sources would initiate specific threat events and the likelihood that the threat events would be successful
- Determine the adverse impacts to the organizational operations and assets, individuals, other organizations, and the Nation resulting front he exploitation of vulnerabilities by threat sources (through specific threat events (through specific threat events); and
- Determine information security risks as a combination of likelihood of threat exploitation of vulnerabilities and impact of such exploitation, including any uncertainties associated with the risk determinations.
Step 3: Communicating and Sharing Risk Assessment Information
Involves communicating the assessment results and sharing risk-related information to decision makers. Communicating and sharing information consists of the following specific tasks:
- Communicate the risk assessment results; and
- Share information developed in the execution of the risk assessment, to support other risk management activities.
Communicate Risk Assessment Results
Communicate risk assessment results to organizational decision makers to support risk responses.
Share Risk-Related Information
Share risk-related information produced during the risk assessment with appropriate organizational personnel.
Step 4: Maintain the Assessment
Maintaining the risk assessment refers to keeping current, and specific knowledge of the risks faced by the organization. The results of the assessment are used to inform risk management decisions and risk responses: acquisition decisions, authorization decisions for information systems and common controls, and connection decisions. Maintaining risk assessments includes the following tasks:
- Monitor risk factors identified in risk assessment on an ongoing basis and understanding subsequent changes to those factors; and
- Update the components of risk assessments reflecting the monitoring activities carried out by organizations.
Monitor Risk Factors
Conduct ongoing monitoring of the risk factors that contribute to changes in risk to organizational operations and assets, individuals, other organizations, or the Nation.
Update Risk Assessment
Update existing risk assessment using the results from ongoing monitoring of risk factors.
NIST SP 800-61 “Computer Security Incident Handling Guide
- Preparation
- Detection & Analysis
- Containment, Eradication, & Recovery
- Post-Incident Activity
Functional Impact Categories
- None – No effect to the organization’s ability to provide all services to all users
- Low – Minimal effect; the the organization can still provide all critical services to all users but has lost efficiency
- Medium – Organization has lost the ability to provide a critical service to a subset of system users
- High – Organization is no longer able to provide some critical services to any users
Information Impact Categories
- None – No information was exfiltrated, changed, deleted, or otherwise compromised
- Privacy breach – Sensitive personally identifiable information (PII) of taxpayers, employees, beneficiaries, etc. was accessed or exfiltrated
- Proprietary Breach – Unclassified proprietary information, such as protected critical infrastructure information (PCII), was accessed or exfiltrated
- Integrity Loss – Sensitive or proprietary information was changed or deleted
Recoverability Effort Categories
- Regular – Time to recovery is predictable with existing resources
- Supplemented – Time to recovery is predictable with additional resources
- Extended – Time to recovery is unpredictable; additional resources and outside help are needed
- Not Recoverable – Recovery from the incident is not possible (e.g., sensitive data exfiltrated and posted publicly); launch an investigation
NIST SP 800-88 “Guidelines for Media Sanitization
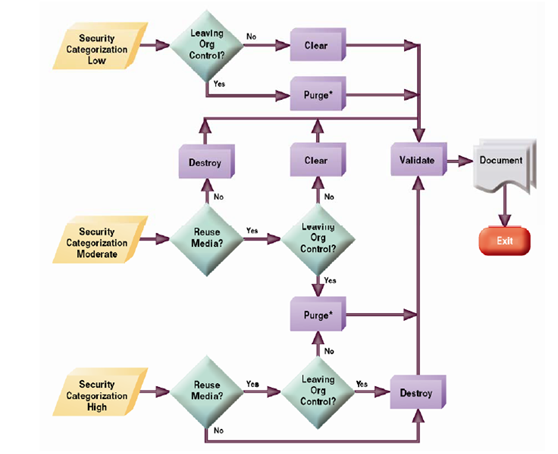
Figure 9.3.2 Sanitization and disposition decision flow
Source: NIST SP 800-88: Guidelines for Media Sanitization
European Regulations on information security
The European Union (EU) has several regulations in place that address the issue of information security. These regulations aim to protect the personal data of individuals within the EU and to ensure that organizations that collect, use, or personal process data do so in a way that is compliant with the law. The most significant of these regulations is the General Data Protection Regulation (GDPR), which came into effect in 2018.
The GDPR sets out strict rules for personal data and gives individuals more control over their personal information. Other necessary EU regulations on information security include the Network and Information Systems Directive, which applies to operators of essential services and digital service providers, and the Cybersecurity Act, which establishes a framework for cooperation on cybersecurity between EU member states. These regulations ensure that information is secure, and that individuals’ privacy gets protected in the digital age.
GDPR
The General Data Protection Regulation (GDPR) protects all individuals within the European Union (EU) and the European Economic Area (EEA) against data breaches. However, it is also possible for organizations outside the EU to process the personal data of EU citizens. Therefore, as well as strengthening and building on the existing data protection framework in the EU, GDPR gives individuals greater control over their personal information. Furthermore, the GDPR imposes stricter rules on organizations that collect, use, or process personal data and higher fines for noncompliance.
Source:
Video:
The new EU General Data Protection Regulation in Under 60 Minutes!
Network and Information Systems Directive (NIS2)
NISD (Network and Information Systems Directive) is a directive of the European Union (EU) adopted in 2016. The goal is to improve the security and resilience of critical infrastructure in the EU and to ensure that operators of essential services and digital service providers have adequate measures to protect their systems and networks.
The NISD applies to many sectors, such as energy, transport, health, and finance, and requires organizations to respond appropriately to protect against cyber-attacks and other security incidents. Also established by the NISD is a network of cooperation between EU member states to exchange information on security threats and incidents and coordinate responses. Cybersecurity and critical infrastructure protection are integral to the EU’s cybersecurity strategy.
Source:
NIS Directive | Shaping Europe’s digital future
Digital Operational Resilience Act (DORA)
Digital operational resilience is the ability of an organization to maintain and recover its critical business functions in the face of digital disruptions such as cyber-attacks, data breaches, and system failures. In the financial sector, digital operational resilience is significant due to the critical role financial services play in the economy and the increasing dependence of financial institutions on digital technologies. As a result, financial institutions must implement appropriate measures to ensure that their operations are resilient to digital disruptions and that they can continue providing essential services to their customers even in the face of such disruptions. It includes having robust and tested incident response plans and effective governance and management processes for digital risk.
Source:
Digital operational resilience act (DORA) | Think Tank | European Parliament
Cybersecurity Standard
The International Organization for Standardization and the International Electrotechnical Commission published the ISO standard jointly in 2005, and the most recent revision was published in 2013.
Payment Card Industry Data Security Standard (PCI DSS)
PCI DSS is a set of security requirements to ensure that all companies that take, process, store, and transmit credit card information maintain an effective security program. To protect their customers’ sensitive information, major credit card companies, including Visa, Mastercard, American Express, and Discover, created these standards to protect their customers’ sensitive information. PCI DSS applies to any organization that accepts, processes, stores, or transmits credit card information, regardless of its size or the number of transactions it processes. Organizations must comply with PCI DSS to protect their customers’ information and avoid potential fines and other penalties.
Source:
Video:
Understanding PCI DSS Webinar with Dr Aftab Rizvi
The HIPAA Act
In 1996, the United States federal law Health Insurance Portability and Accountability Act (HIPAA) was enacted, establishing standards for protecting and disclosing certain health information. The HIPAA law applies to many health care providers, health plans, and other entities that handle personal health information. Compliance with HIPAA is mandatory for covered entities, and noncompliance can result in significant penalties. HIPAA protects the privacy of an individual’s health information and ensures that it gets used appropriately.
Source :
Cyber Security Guidance Material | HHS.gov
The full text for HIPAA compliance consists of (45 CFR parts 160, 162, and 164). NIST SP 800-66r2 “Implementing the Health Insurance Portability and Accountability Act (HIPAA) Security Rule” provides the specifications for implementing HIPAA. The NIST HIPAA Crosswalk maps the HIPAA requirements outlined in 45 CFR to NIST CSF’s Five Core Functions.
One of the best resources for HIPPA is from the U.S. Department of Health & Human Services’ Health Information Privacy (HHS). The HHS frequently releases updates to HIPAA for Professionals.
To help cybersecurity professionals audit their network, NIST has released a SCAP module for HIPAA: HIPAA Security Rule Toolkit. However, it is no longer being maintained.
Overview
Privacy Rule – Who is Covered?
- Health Plans
- Health Care Providers
- Health Care Clearinghouses
Privacy Rule – What is Covered?
- The individual’s past, present, or future physical or mental health or condition
- The provision of health care to the individual, or
- The past, present, or future payment for the provision of health care to the individual
Security Rule – What is it?
“The Security Rule requires covered entities to maintain reasonable and appropriate administrative, technical, and physical safeguards for protecting e-PHI. Specifically, covered entities must:”
- Ensure the confidentiality, integrity, and availability of all e-PHI they create, receive, maintain or transmit.
- Identify and protect against reasonably anticipated threats to the security or integrity of the information.
- Protect against reasonably anticipated, impermissible uses or disclosures; and
- Ensure compliance by their workforce.
Administrative Safeguards
- Security Management Process
- Security Personnel
- Information Access Management
- Workforce Training and Management
- Evaluation
Physical Safeguards
- Facility Access and Control
- Workstation and Device Security
Technical Safeguards
- Access Control
- Audit Controls
- Integrity Controls
- Transmission Security
HSSE and Social Performance
Constantia Flexibles must optimize customer Value while protecting people, assets, the environment, and reputation to succeed long-term. The management of health, safety, security, and the environment (HSSE) and social performance is a priority for many organizations. Health, safety, security, and environmental management manage risks and impacts associated with an organization’s operations. The following points are key to the framework.
- Health
- Safety
- Security
- Environment
- Pursue the goal of no harm to people.
Source:
Commitments, policies and standards | Shell Global
The SOC control standards
The American Institute of Certified Public Accountants (AICPA) represents public accountants in the United States. Organizations can assess and improve their cybersecurity posture with the help of cybersecurity audits offered by the AICPA, one of its services.
An organization’s systems, networks, and data get analyzed during a cybersecurity audit. A technical assessment of the organization’s systems and networks may also get included in the audit, along with reviewing cybersecurity policies, procedures, and controls.
As part of a cybersecurity audit, vulnerabilities and weaknesses are identified, and recommendations for improving security are made. Among the cybersecurity audit services offered by the AICPA is the Cybersecurity Risk Management Reporting Framework (CRMRF) and the System and Organization Controls for Cybersecurity (SOC). There are different SOC types in SOC.
- SOC 1
- It relates to the internal control of financial reports in service organizations
- SOC 2
- Information system security, availability, processing integrity, and confidentiality get evaluated in this report. As part of a SOC 2 Type I audit, the auditor reviews the “design” of the program at a point in time. In most cases, the auditor will examine a single example of each control working effectively to demonstrate the existence of a process. In the event of a SOC 2 Type I audit, the company will receive a report as soon as possible and can be confident that the implemented controls will survive the SOC 2 audit.
- A SOC 2 Type II audit assesses controls “operating effectively” for a defined period (usually 12 months)
- A SOC 2 Type II audit involves
- Walkthroughs with the controlling owner
- Requesting and reviewing 100s of audit artifacts to gain assurance controls are in place
- Information system security, availability, processing integrity, and confidentiality get evaluated in this report. As part of a SOC 2 Type I audit, the auditor reviews the “design” of the program at a point in time. In most cases, the auditor will examine a single example of each control working effectively to demonstrate the existence of a process. In the event of a SOC 2 Type I audit, the company will receive a report as soon as possible and can be confident that the implemented controls will survive the SOC 2 audit.
- SOC 3
- Unlike SOC 1 and SOC 2, the SOC 3 report does not provide detailed information
Scope
The first step is to decide on the scope of the SOC 2 program.It can be the entire organization or part of it. The driver of the scope depends on the objectives we are trying to meet. For example, it may include the whole or only part of the organization. Nevertheless, remember that certain corporate functions like HR, Corporate IT, and Legal will likely fall in scope no matter what.
Design controls
In contrast to many other frameworks, SOC 2 does not impose rigid controls. Instead, it establishes standards that organizations must meet, and organizations can describe how their processes are consistent with those standards. Thus, the audit burden will be reduced, and the audit will reflect the reality of the environment.
Program implementation
Finally, we will need to build the program. Common items include:
- Establishing a governance structure
- Policies
- Risk assessment
- Internal security assessments
- controls spot checks
- penetration testing
- third-party security
- Cleaning up user access
- Formalizing the Software development Life Cycle
- Implementing a vendor risk management program
SOC 2 does not pass/fail. The organization will get a SOC 2 report even if the auditor finds many issues. Anything that the auditor finds will get disclosed in the report.
Source:
System and Organization Controls: SOC Suite of Services | Resources | AICPA
Video: