Network Threats
When we talk about a network, we talk about computer networks. In this subchapter we will talk about all the different network attack vectors an attacker could use to compromise the network and damage your business operations and business continuity. We must be going to name only some of the different attack vectors. Still, you must have a global idea of the different network threats you may face as a blue or purple teamer or, of course, when you joined the dark side as the red team as an adversary emulation.
Denial Of Service (DOS)
A DOS attack usually denies the service of a network or application. While the attacker performs a Denial of Service attack, it will overload or stress the network or application so much it will not be able to be responsible or respond to requests from legitimate users. To mitigate these attacks, it is essential to remember to have your applications patched and apply a firewall at your network entry points. DOS can also be triggered by executing a payload to the target that will make the application crash; this could also cause DOS.
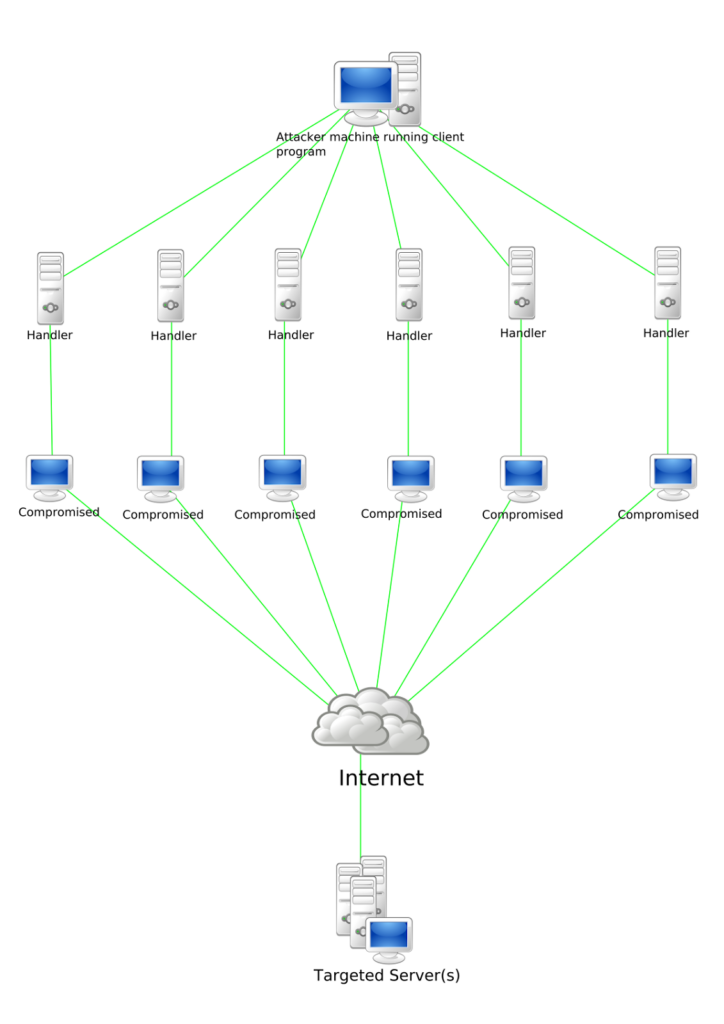
Distributed Denial of Service (DDOS)
During a DDOS attack, multiple bots or computers will target the same network or web application endpoint to cause a denial of service. The best mitigation for DDOS attacks is to have a solid web proxy and Content delivery networks in place to mitigate loads of such attacks. DDOS attacks could put up to terabytes a second, which could go even down the most prestigious firewalls out of commission. Once the pipe is clogged with junk data, there is not much you can do besides sending the traffic into a black hole.
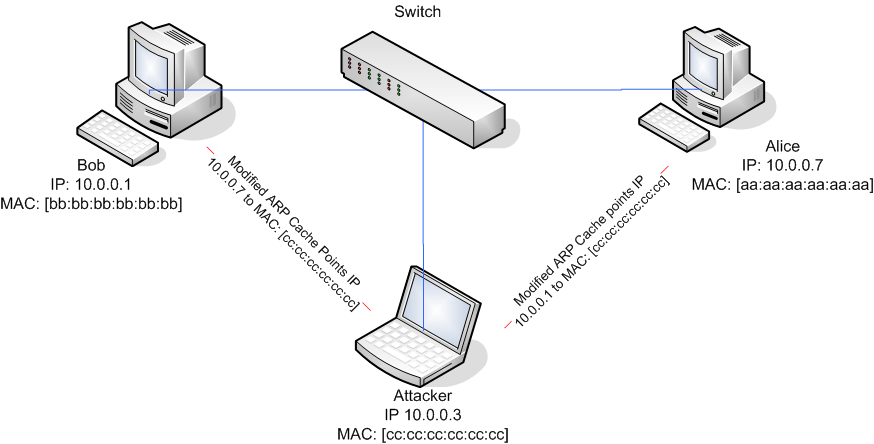
14.3. Address Resolution Protocol Poisoning (ARP)
This attack usually allows the attacker to intercept or modify packets or redirect traffic to him. This is a very dangerous attack type because it could allow you to send credentials or intercept web traffic and modify it. The best protection against such attacks is implementing NLA or network-level authentication before a device is allowed on network
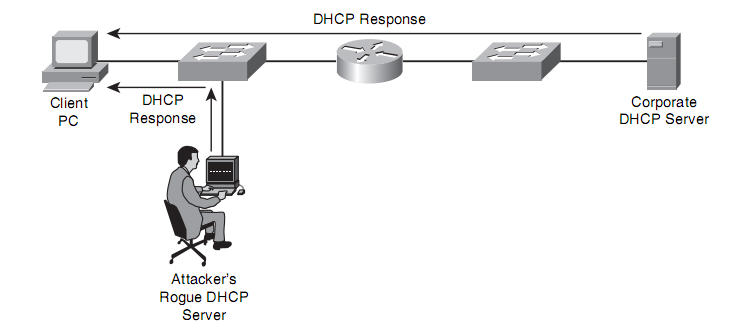
14.4. Rogue Dynamic Host Configuration Protocol Server (DHCP)
On almost every network, you will find a DHCP server. If the network administrators allow fake DHCP servers to be on the network, it could allow attackers to redirect, modify or steal credentials. It is always a good idea to block unauthorized DHCP packets for either IPv4 and IPv6. Besides that, network-level authentication (NLA) should help prevent these kinds of attacks.
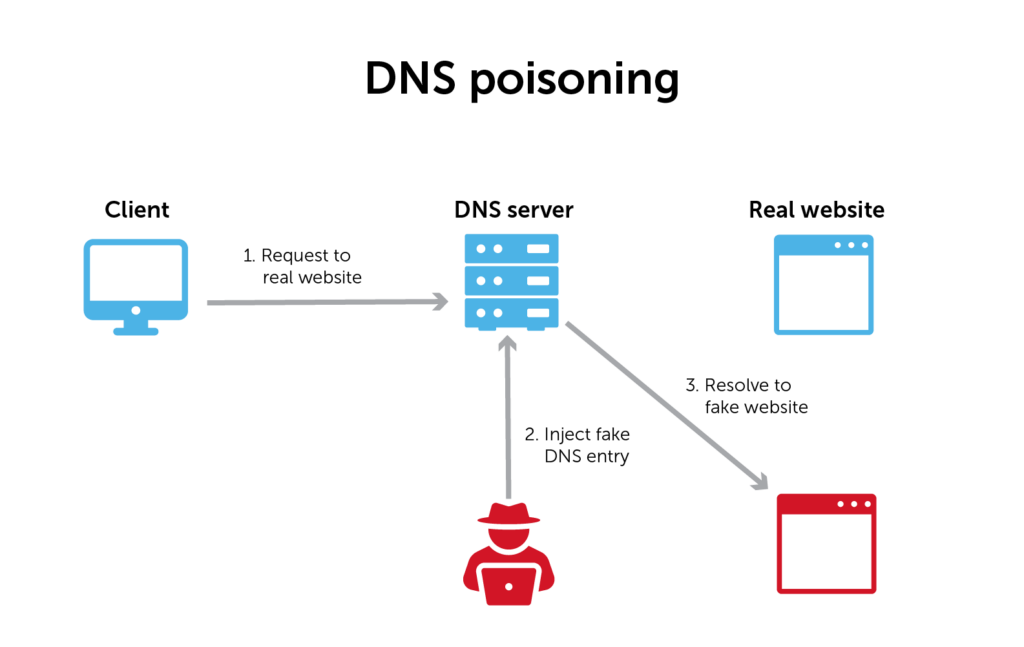
14.5. Domain Naming Service cache spoofing (DNS)
Even though our DNS service is not free from attacks, in the last few decades, DNS attacks have been more prevalent. These attacks allow the attacker to poison the DNS entry table of the computer system and send network traffic to a different web server than the authoritative intended. The best way to mitigate such attacks is to implement Domain Name System Security Extensions and not allow domain spoofing within your enterprise domain network. While also protecting from domain takeovers, it is recommended to protect your domain registrar with 2-factor authentication.
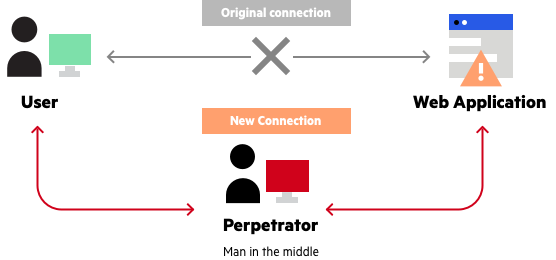
14.6. Man in the middle attacks (MitM)
These attacks allow the hacker to flow traffic through his computer, allowing him to inspect all the traffic being sent. Usual mitigations for these attacks involve having a Virtual Private Network, and for added protection, websites usually include Transport Layer Security over The Hypertext Transfer Protocol Secure. This can help to protect you against a potential attacker that is traversing your traffic
Most of these attacks have simple mitigations you could apply to your network. To further understand the amount of different attacks we use MITRE attack to map out all the different attack vectors.
Source:
Denial-of-service attack – Wikipedia
https://en.wikipedia.org/wiki/DNS_spoofing
Man-in-the-middle attack – Wikipedia
Analyzing Quantum Insert Attacks | Infosec Resources
Spanning Tree Protocol – Wikipedia
Instructional and tutorial Videos:
ARP Poisoning or ARP Spoofing Attack – Explanation & Demonstration
ARP Explained – Address Resolution Protocol
DHCP Explained – Dynamic Host Configuration Protocol
Rogue DHCP Server | Man-in-the-Middle Attack