the use of firewalls
Allows us to control what enters or leaves a network and what enters or leaves a computer. It is possible to set rules on these firewalls to dictate what kind of traffic leaves our networks, what kind of traffic leaves our computers, and what kind of traffic comes into our computers.
Confidentiality of the network
There would be no point in having the server within an internal network if it were not accessible to Internet users. Another attack could use that server to steal data and get into other systems or servers in the network if it existed. Therefore, the server must be placed between two firewalls so that it can get accessed from the internet.
Demilitarized Zone (DMZ)
This problem is not affected by the location of the demilitarized zone. Therefore, using a back-to-back firewall strategy could resolve it. Here is an example of a commercial organization. The internet is the external network, and here is the internal network. Our organization utilizes an internal network of computers, users, and staff in addition to the internet. The firewall can be used for the public and by filtering or protecting applications. An examination of packets is another possibility.
Source:
Packet inspection firewalls
The firewall blocks traffic from entering or leaving the network if a rule is triggered. If no rules are triggered, the firewall will allow all traffic, whether inbound or outbound. In addition, firewalls filter applications. Firewalls that look at what applications are being called upon by traffic. Applications that shouldn’t, the firewall, will prevent such communications. As a result, communications do not get to the end server.
Stateful firewalls
Incoming traffic can be determined when full-state firewalls receive incoming replies. Firewalls can get used to
- Protect the network
- Implement network rules
- Limit traffic to specific routes
They can also get used for constructing Demilitarized Zones. Using virtual area networks for routing and switching different networks is a standard feature of modern configuration networks.
Application Filter
Through application filtering, this firewall can see what kinds of applications get called and what commands are issued by public users attempting to access the web server. It could also inspect every packet to ensure malicious content is never brought onto the web server. For instance, our firewalls can get configured to filter applications or inspect packets.
Only this server can get controlled by users on the internet who can access the web server, but they cannot access this network because of these firewalls. Demilitarized zones are what we call them. DMZs are secure areas of the network where only trusted users are allowed. In today’s world, this is especially important. In some organizations, web servers get located in the DMZ. Other organizations put their email servers in the DMZ. Users on the internal network and those working can access the website. However, care gets taken to ensure they cannot get into the network using these firewalls.
When malicious people attack the network, they try to cripple the firewalls. That way, they can try to defeat the organization’s defenses. The firewall explains the definition of the first line of defense between the internal network and the external network.
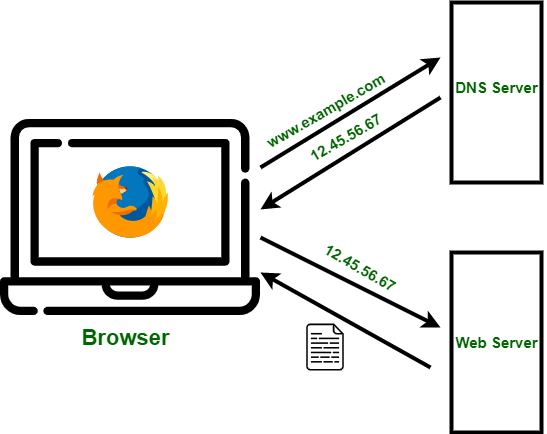
DNS (Domain Name System)
Is a distributed database that maps domain names (such as www.example.com) to IP addresses. It allows users to access websites and other resources using easy-to-remember names instead of numerical addresses.
File sharing
Refers to distributing and accessing digital files over a network, such as the Internet. This can be done through various methods, including peer-to-peer networks, cloud storage services, and file-hosting websites.
Common Web protocols
Hypertext Transfer Protocol or Hypertext Transfer Protocol secure. is a protocol for transferring data over the Internet, such as web pages and other resources. It is the foundation of the World Wide Web and browsers to communicate with web servers. Common web protocols include HTTP
- HTTP
- HTTPS (a secure version of HTTP)
- FTP (File Transfer Protocol)
- SMTP (Simple Mail Transfer Protocol)
These protocols facilitate different types of communication and data transfer over the Internet. HTTPS uses encryption and is an entirely new protocol. The most common command standard for it now is using TLS 1.0 to TLS 1.3. TLS stands for transport layer security. Most companies provide services like;
- Payment
- Banking
- Shopping
- Storing user information
- Social Media Networks
- Cloud storage
Will be enforced to protect our data. To combat this we use encryption to make it harder for cyber-criminals to read the network traffic if they intercept the connection.