Detection Engineering
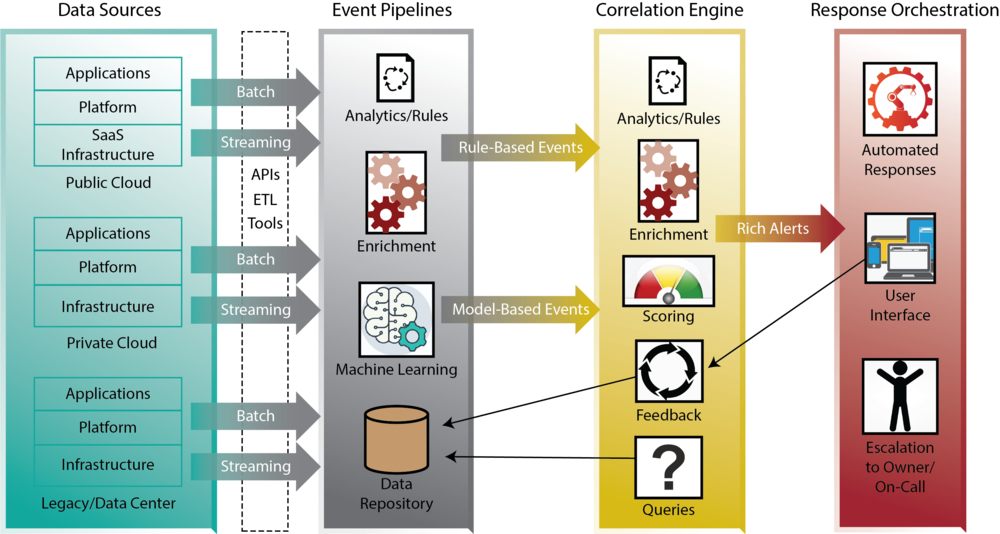
is the process of designing, developing, and implementing methods for detecting potential security threats or incidents. It can involve various tools and techniques, such as intrusion detection systems (IDS), network traffic analysis, or data analytics. The goal of detection engineering is to identify potential security threats or incidents as early as possible, so that appropriate action can be taken to prevent or mitigate the impact of the threat.
Detection engineering typically involves several key steps, such as defining the detection process’s scope and objectives, identifying potential data sources that can be used for detection, developing appropriate detection methods and algorithms, and implementing and testing the detection system. It can involve working closely with other teams, such as security operations, incident response, or threat intelligence, to ensure that the detection system is effective and provides the necessary information for response and mitigation. The monitoring and evaluation of the detection system to ensure that it continues to be effective and to make any necessary adjustments or improvements. There are common ways to detect threats.
Source:
https://detectionengineering.io
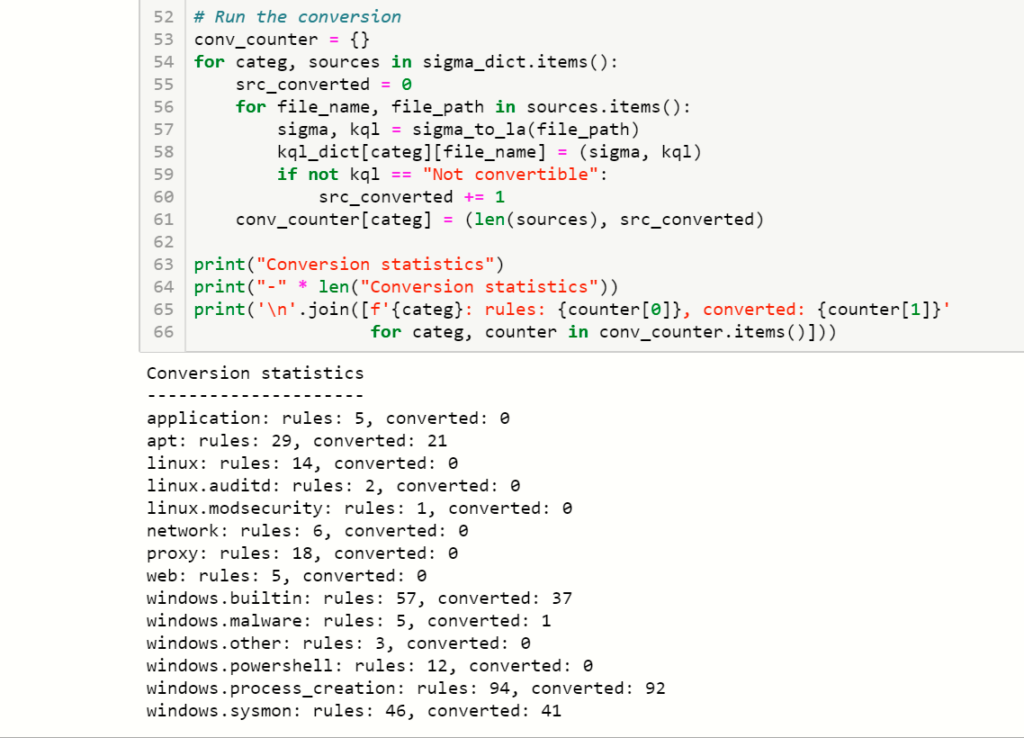
Sigma
Sigma is a generic and open-source rule format that allows users to write rules simply and concisely. Sigma rules can detect various security-related events, such as network intrusions, system misconfigurations, or malicious activity. Sigma rules are typically written in the YAML format and combine search patterns, conditions, and logical operators.
Source:
Learn How to Write Sigma Rules Efficiently | Medium
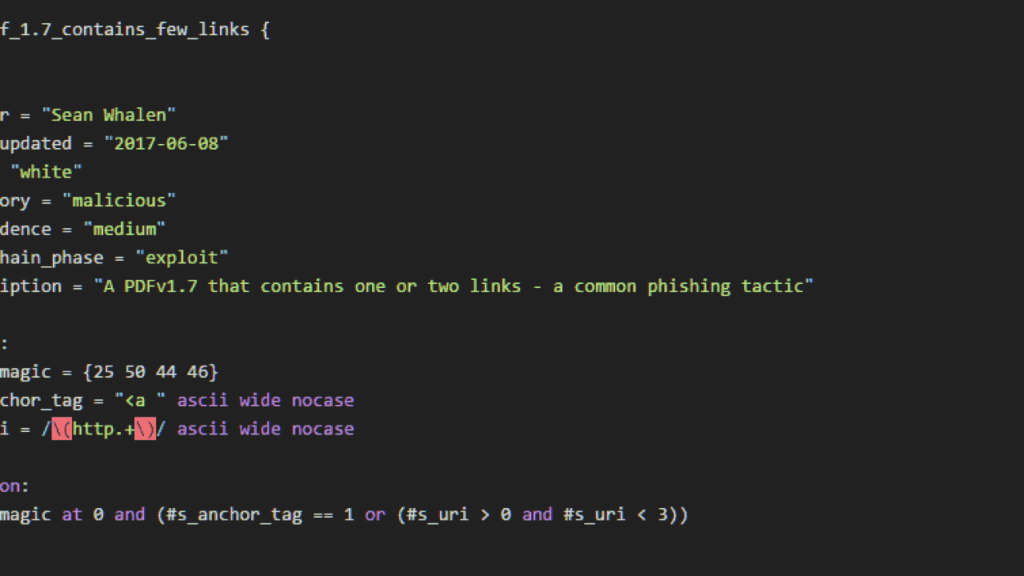
Yara
Yara is a tool that allows users to create their own rules for identifying and categorizing malware samples. These rules can be based on various characteristics, such as file metadata, strings, or hexadecimal patterns. Yara rules get written in a simple yet powerful language that allows users to specify complex patterns and conditions for identifying malware. Yara rules can be used with other malware detection tools, such as antivirus software or sandbox environments, to improve the accuracy and effectiveness of malware detection.
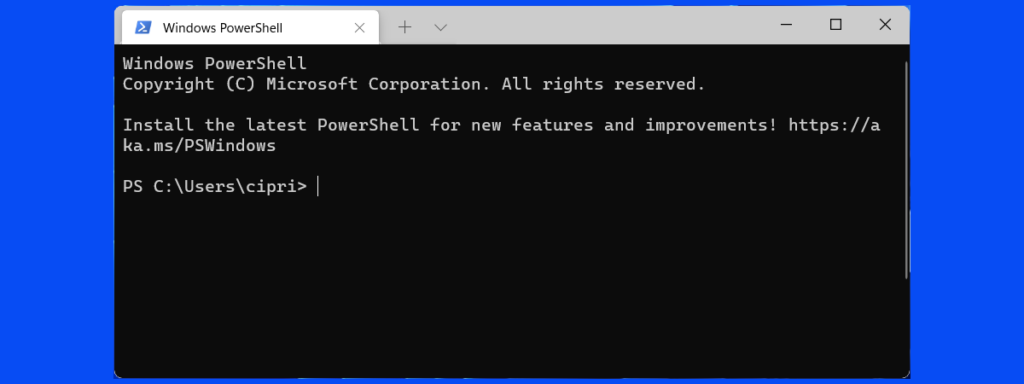
PowerShell
Is a powerful scripting language and automation platform that can be used for various detection engineering tasks. For example, PowerShell can automate the collecting and analyzing log data from various sources, such as security event logs, network traffic logs, or system configuration data. It can help to quickly and efficiently identify potential security threats or incidents.
Reverse engineering and dynamic analysis of software
To detect any potential indicators of malicious activity, tools get used to examine the behavior of programs and processes. For example, IDA and Ghidra can get used to disassembling and analyzing binary executables. On the other hand, Process Hacker and API Monitor are used to monitor how processes behave and interact with system APIs. Among the tools used to monitor and analyze network and system activity are called
- Sysmon
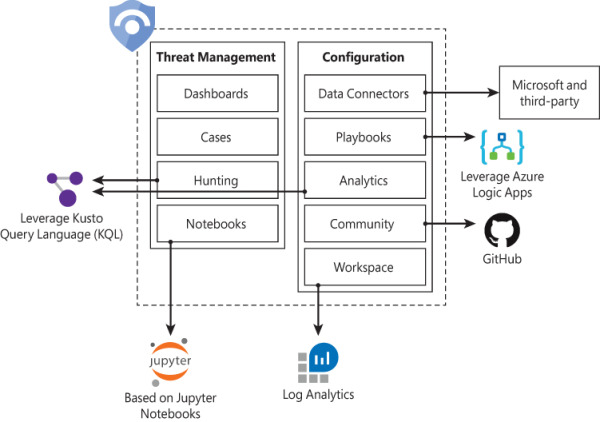
- Azure Sentinel
- Defender for Endpoint
It is possible to identify potential indicators of malicious activity with these tools, and they can provide detailed insight into the behavior of systems and processes. In addition to monitoring and logging system and network activity on individual machines, Sysmon and Azure Sentinel can provide centralized monitoring and analysis capabilities at the network and enterprise levels. It is possible to use these tools to improve the accuracy and effectiveness of detection systems and provide valuable data for detection engineering.